Today I want to discuss one of the biggest personal data breaches in history – Collection #1, which occurred at the beginning of 2019.
Collection #1 is a set of email addresses and passwords totaling 2,692,818,238 rows. However, in total there are 1,160,253,228 unique combinations of email addresses and rehashed passwords. It’s made up of many different individual data breaches from literally thousands of different sources.
The breach was first revealed by security researcher Troy Hunt who runs the service “Have I been pwned”. Soon after revealing Collection #1 he added more than 7 hundred thousand new unique email and password combinations. You can also use this service to check whether your password is there.
Personally I checked my email addresses and one of them happened to be hacked. Despite changing all my passwords every half a year and most likely my older password was breached, it still impacted my sense of security.
However the danger of Collection #1 lies not in the amount of data, but in the way it can be used. The easiest and most popular usage is obviously blackmailing. Here you can see an example of a phishing email that many people received soon after Collection #1 breach.
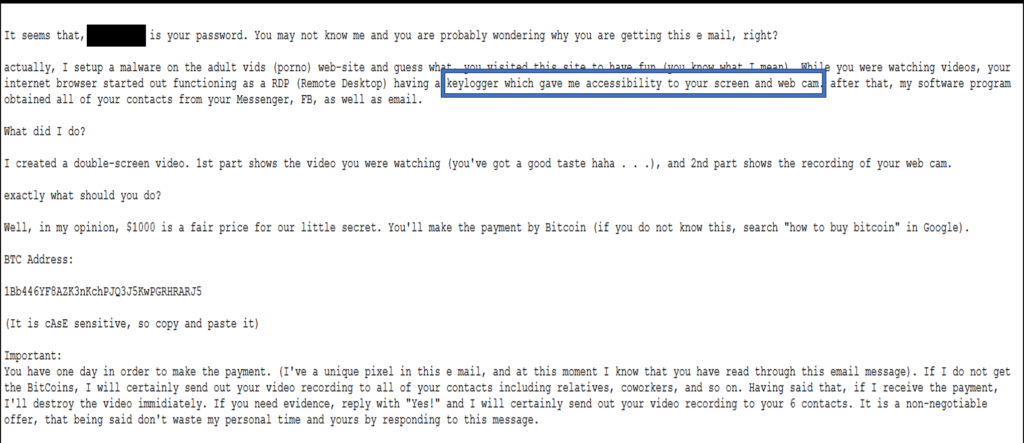
As you can see, the email contains a user password and looks quite convincing. However, those of you who are at least somewhat familiar with cyberattacks should spot at least one weird thing. That’s the keylogger description. Keyloggers don’t function this way.
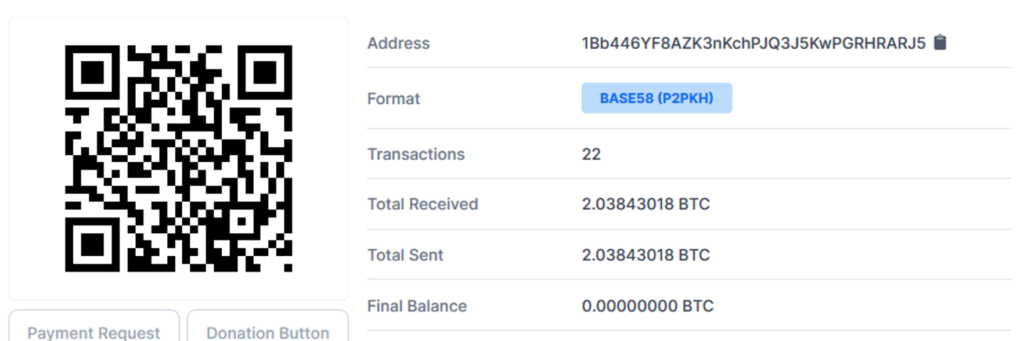
Moreover, as all bitcoin transactions can be found in free public access, we can also take a look how much did this hacker earn. As you can see, 2.2 bitcoins, which is 12000$ at the time of the attack.
Now let’s think for a while how this attack can be implemented. First of all, it is impossible to send 2 billion emails without getting banned by the email provider. So, first of all the attacker has to narrow down the amount of emails. As Collection #1 is a collection of various data breaches, many email:password combos are likely not valid. So, first of all, the attacker needs to validate passwords. This can easily be done for example with atlantr, a tool written in python and available on GitHub. After that, the attacker has to send emails to users, which can easily be done with a simple php script.
It is very important to know not only how hackers are trying to fool you but also how you can protect yourself!
Some simple steps you can take include:
- Turn off your web cameras when you are not using them. Hackers can gain access to your camera and record activity without you knowing.
- Do not open attachments from people you do not know.
- Never send sexual or images of yourself to anyone, no matter how long you know them and how much you trust them. Save that for in person. This is especially true for someone you do not know well.
In conclusion, I would like to note that basic knowledge in e-Security is important in the digital society in which we are living today.